This article was published as a part of the Data Science Blogathon.
Blockchain has the ability to change many things about the banking and financial systems, digital art, smart contracts, and so on. From a commercial standpoint, we can think about blockchain technology as a new breed of business process improvement software. Blockchain and other collaborative technologies promise to significantly reduce the “cost of trust” by enhancing the commercial activities that take place between firms. But this needs to be secure. This is where cryptography comes into place.
Cryptography enables safe communication in the presence of malevolent third parties, referred to as adversaries. Encryption transforms an input (i.e., plaintext) into an encrypted output using an algorithm and a key (i.e., ciphertext). A given algorithm will always turn the same plaintext into the same ciphertext if the same key is utilized. An algorithm is considered secure if an attacker cannot deduce any properties of the plaintext or key from the ciphertext. Given a large number of plaintext/ciphertext combinations that used the key, an attacker should be unable to deduce anything about the key.
Source: https://www.michalsons.com/blog/cryptography-laws-in-south-africa/3266
Cryptography techniques are derived from mathematical principles and a collection of rule-based calculations known as algorithms to change messages in ways that make them difficult to decode. These algorithms generate cryptographic keys, digitally sign documents, verify data privacy, and safeguard secret transactions such as credit card and debit card transactions.
Some features of Cryptography are as follows:
Cryptography can protect the confidentiality and integrity of data both in transit and at rest. It can also authenticate senders and recipients and guard against repudiation.
Software systems have many endpoints, multiple clients, and one or more back-end servers. These client/server communications take place across untrustworthy networks. Communication occurs across open, public networks like the Internet or private networks that external attackers or bad insiders can hack.
Cryptographic protocols such as SSL/TLS provide confidentiality and integrity protections for communications, preventing malicious eavesdropping and tampering. Authentication safeguards ensure that users are communicating with the systems as intended. Are you, for example, giving your online banking password to your bank or to someone else?
It can also be used to secure data in transit. Data on a detachable disc or in a database can be encrypted to prevent disclosing sensitive data if the physical medium is lost or stolen. Furthermore, it can provide data integrity protection at rest to identify malicious manipulation.
Cryptography is a technique for protecting data from unauthorized access. Cryptography is used in blockchain to safeguard transactions between two nodes in a blockchain network. As previously stated, the two essential concepts in a blockchain are cryptography and hashing. In a P2P network, cryptography is used to encrypt messages, while hashing is used to protect block information and link blocks in a blockchain.

Source: https://engineering.tamu.edu/news/2022/05/csce-cryptography-in-the-blockchain-era.html
The primary goal of cryptography is to ensure the security of participants and transactions and safeguard against double-spending. It aids in the security of various transactions on the blockchain network. It assures that only the person supposed to receive, read, and process the transaction data may do so.
A distributed ledger system with a point-to-point network cannot function successfully or safely unless a strong security technique is in place. Blockchain employs two sorts of security methods: cryptography and hashing. The main distinction is that cryptography encrypts messages in a P2P (Point-to-Point) network. On the other hand, hacking is used to safeguard block information and connect blocks in a blockchain.
The main emphasis of blockchain cryptography applications is on concepts like encryption, decoding, cyphers, and keys. The cypher algorithm executes the encryption and decryption procedures, often through predetermined steps.
There are mainly two types of cryptography. Let us discuss them.
It focuses on a similar key for both encryption and decryption. The symmetric key encryption approach can also be used to safeguard website connections or data encryption. It is also known as secret-key cryptography. The only issue is that the sender and receiver must exchange keys securely. Data Encryption Technology is a well-known symmetric-key encryption system (DES). The cryptographic technique encrypts the data using the key in a cypher, and the data must be accessible. The data can be decrypted by someone with access to the secret key. Examples include AES, DES, and others.
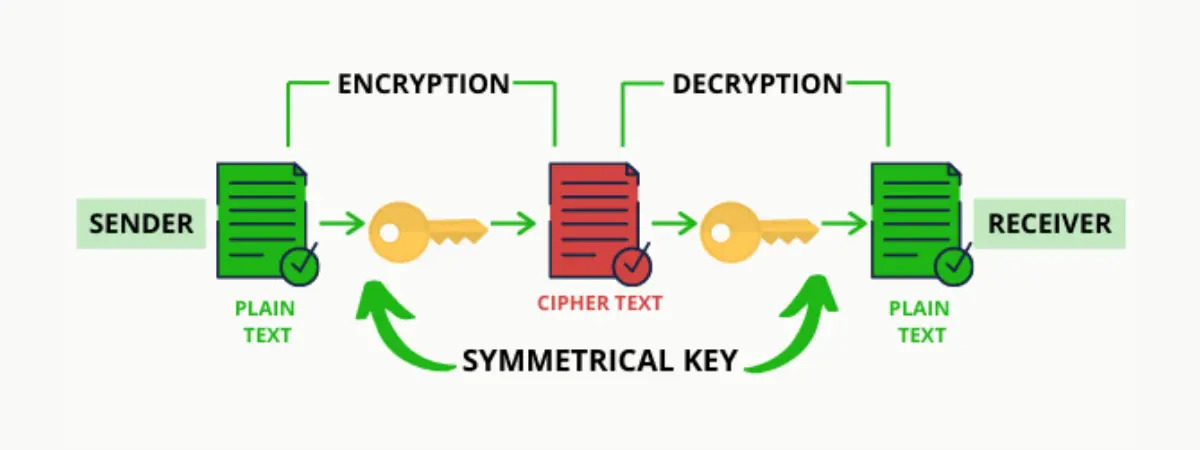
Source: https://101blockchains.com/blockchain-cryptography/
Despite being the fastest technique, one big disadvantage is that a node will need many keys to interact with other nodes in the network. Furthermore, the nodes must ensure that they securely share the key, or a third node may obtain it. Because of these limitations, another type of asymmetric key cryptography emerged.
This cryptography approach employs various keys for encryption and decoding. This encryption method employs both public and private key techniques. This public key mechanism allows unknown individuals to share information like email addresses.
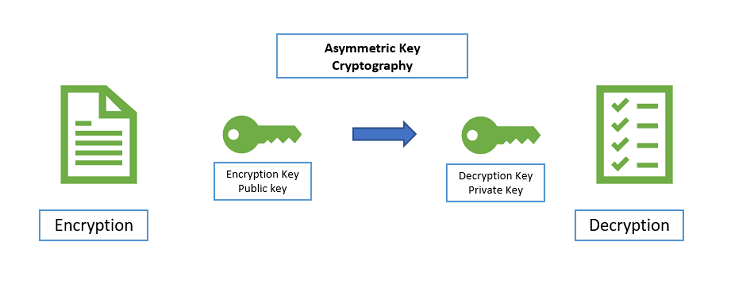
Source: https://cheapsslsecurity.com/blog/what-is-asymmetric-encryption-understand-with-simple-examples/
The private key aids in the decryption of messages and the verification of digital signatures. The private key cannot be deduced from the public key, but the public key can be derived from the private key according to the mathematical relationship between the keys. ECC, DSS, and so forth.
Cryptographic hashing is a well-known application of cryptography. Immutability in the blockchain is enabled by hashing. Keys are not used in the encryption of cryptographic hashing. When a transaction is validated, the hash algorithm adds the hash to the block and creates a new unique hash from the original transaction. Although hashing continues to combine or create new hashes, the original footprint remains available. The root hash is the single combined hash. The hash function aids in linking blocks and the integrity of data inside blocks; any changes to the block contents result in a break in the blockchain. MD5 and SHA-1 are two regularly used hashing functions.
Hash algorithms used in cryptography are deterministic. As a result, the hash function always produces an output with the same length, regardless of how many times you enter a certain input. The output would be 32 characters in a fixed string containing a mix of numbers and letters, regardless of whether you entered a string with 3 characters or 200 characters.
The output of cryptographic hash algorithms exhibits the second crucial characteristic, uniqueness. With cryptographic hash functions, you don’t have to be concerned about two different inputs producing the same output. They can therefore provide special functions for preventing any clashes.
An endless number of transactions can be securely stored over the network via cryptographic hashing. Blockchains can keep expanding at scale because several transactions can be combined into a single hash.
With the use of cryptography, we can encrypt data, send cryptocurrency securely, and keep track of past transactions. Blockchain is a modern-age technology that will have many uses. Cryptographic techniques will improve the use of Blockchain.
To summarise:
So we looked at why cryptography is important for blockchain, and we can conclude that blockchain is unstoppable because of cryptography.
The media shown in this article is not owned by Analytics Vidhya and is used at the Author’s discretion.
Lorem ipsum dolor sit amet, consectetur adipiscing elit,